16 years experience and I want to start with cloud security
Hello Andrew I have total 16 years of experience which includes both application development and application security I want to start with cloud security, However, my current organization is not working with cloud in any way and doesn't look like it will for another few years I have experience in application security testing and secure code review I have also completed the CCSK certification
CCSK and Theoretical Cloud Security
For those who are reading, the CSA Certificate of Cloud Security Knowledge (CCSK) is a vendor-neutral cloud security certification that costs $395 USD to sit.
I would not describe it as difficult but being very broad as you can see with the following domains:
- Cloud Computing Concepts and Architectures
- Governance and Enterprise Risk Management
- Legal Issues, Contracts and Electronic Discovery
- Compliance and Audit Management
- Information Governance
- Management Plane and Business Continuity
- Infrastructure Security
- Virtualization and Containers
- Incident Response
- Application Security
- Data Security and Encryption 1.Entitlement, and Access Management
- Security as a Service
- Related Technologies
If you want a good sense of what the CCSK covers at a granular layer look at the table of contents for the CCSK Exam Guide on Amazon
Just like the CompTIA Cloud+, I think there is lots of great knowledge here, but I'm dissuaded to recommend individuals to sit the exam at such a high price point (unless of course your company is willing to pay for it, or you have identified employers who are asking for it as a requirement)
If you can afford the ~$40 USD CSSK Exam Guide on Amazon I consider it a must-read before you start diving into practical cloud security.
I think the CCSK is a lot more useful than the CompTIA Security+. Security+ feels like it's written through the lens of a network engineer, and I feel it's information you'll encounter elsewhere on your journey.
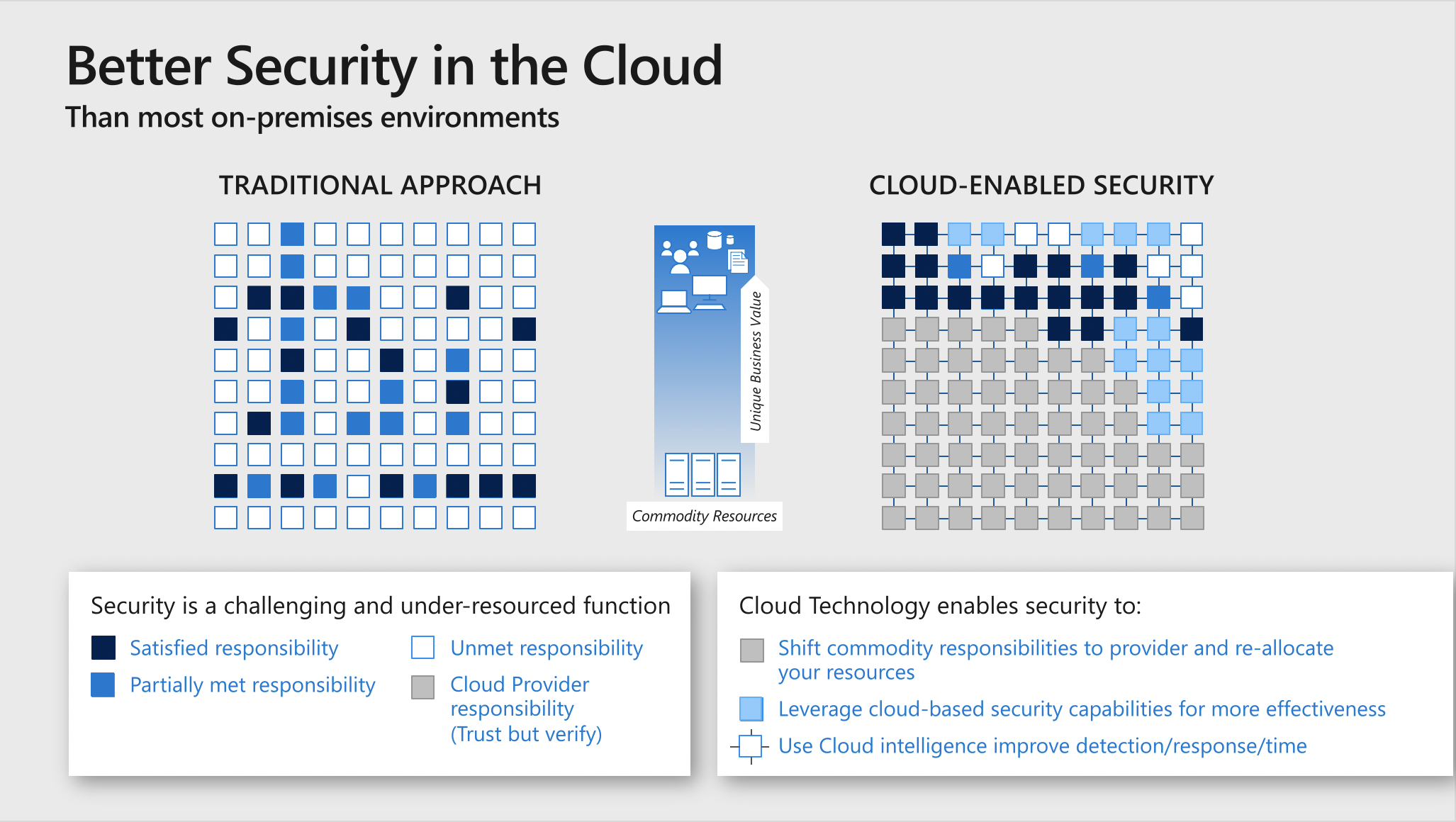
Practical Cloud Security
If you're looking to do Cloud Security the are 4 things you need to gain practical experience within:
- Identity
- Compliance
- Governance
- Security
1. Identity
When you think of Identity I want you to think about the Zero Trust Model.
The Zero Trust Model operates on the principle of “trust no one, verify everything”. It's not a new concept, and honestly, many security experts have lauded the term similar to systems engineers complaining about the term DevOps, for being both broad in scope and hard to define, and just part of the normal job.
The Zero Trust Model is a communication tool to help organizations think differently about their security perimeter and its popularity exploded due to COVID where Work from Home (WFH) became commonplace. Organizations could no longer rely on their physical office computer network to keep their organizational resources secure.
- Microsoft Azure has its own Zero Trust Model which revolves around Azure AD
- Google Cloud has its own Zero Trust Model which revolves around BeyondCorp
- AWS has... well they have an article about Zero Trust Architecture which looks far off from Azure and GCP.
AWS does not have an Identity as a Service (IDasS), Mobile Application Management (MAM) or Mobile Device Management (MDM) like Azure and GCP. AWS hasn't made it clear what third-party provider would be the best to utilize for Identity to implement a Zero Trust Model with your AWS workloads.
For Identity, I strongly recommend studying the SC-900 and Azure AD and learning about BeyondCorp.
2. Compliance
These are the 4 regulatory compliance programs I hear my fellow CTOs or CISOs griping to try and figure out: -SOC2, ISO 27001, FedRamp HIPPA
Having practical experience in regulatory compliance is extremely valuable, however, the only way to obtain this knowledge is if your company is going through the process and you are a key person in that initiative because it's very expensive and involved.
You can learn by proxy by talking to lots of cloud vendors specializing in compliance sitting through as many demos as possible and asking lots of questions.
You will also want to know in practice FIPS 140-2, GDPR, which are more accessible in learning since you can simulate it yourself within your own cloud service provider (CSP) account.
Tugboat Logic and Vanta being the two most popular compliance vendors, so learn about their offerings.
3. Governance
Governance is often accompanied by Compliance and Risk Management (GCR).
Governance is the practice of creating policies, procedures, playbooks, security controls, and guard rails to ensure your organization is meeting your security needs.
So in AWS, governance would be things like how to apply Service Control Policies to AWS Organizations, Adopting GitOps, Infrastructure as Code via CloudFormation, having departments procure cloud resources or workloads through AWS Service Catalog or applying IAM Permission Boundaries to IAM groups and users.
While there are lots of cloud services to support Governance you need to remember Governance is all about dealing with people and utilizing soft skills because no matter the tooling, you need to continuously train your team.
Playbook and Runbooks is something you want to learn how to write, however, you're not going to find any off-the-shelf examples because organizations invent their own. So get creative and design some with your best guess of what a good Playbook or Runbook should look like.
To learn the persuasive art of getting people to push left I recommend consuming large amounts of Mark Nunnikhoven content as a learning model for cloud security communication.
4. Security
For security, we'll take a closer look at each CSP's offerings.
AWS
AWS has three major security deficits:
- A lack of robust Identity features
- A lack of built-in visibility for assesing Security Posture
- Poor assets and inventory management
So you really need to lean on third-party providers to meet your organization's security needs. So maybe you would use:
- JumpCloud as an agnostic Identity as a Service (IDaaS)
- JupiterOne for Graph-powered Cloud Asset/Inventory Management (CAM)
- Very Good Security to generate Security Scores
The hardest challenge is determining a good AWS Multi-account strategy. Unlike GCP and Azure, AWS is unique where there is lots of friction to create isolate workloads. There is AWS Control Tower that can set you up with AWS's best practices for multi-account and allow you to self-vendor new accounts but in practice, AWS Control Tower is not a one-size-fits-all so most companies are rolling their own strategies.
AWS Security Speciality
This certification focuses on the utility of AWS security services and it would be better to name this certification the AWS DevSecOps Speciality.
Although being a Speciality course its lacking lots of cloud security knowledge, and securing AWS really relies on utilizing third-party security vendors.
The CCSK would be a very useful precursor before taking this exam.
Microsoft's Active Directory is not really covered by AWS but because it's so prevalent in the industry there are many questions involving Active Directory on the exam.
This is why I would recommend spending time on Microsoft Azure learning Active Directory through Azure AD via the SC-900.
re:Inforce
AWS has an AWS Security convention called re:Inforce. It's more people wearing t-shirts than suits (unlike most security conferences) and there are lots of hands-on activities to gain practical AWS security knowledge.
It's very expensive but if you have the opportunity to go, it is well worth the investment.
Even though it's an AWS event all the security vendors are present and they're all secretly dying to talk about their multi-cloud offering so you can pick up lots of transferable knowledge to apply to any Cloud Service Provider (CSP).
AWS Security, Identity, and Compliance
AWS has a 3-hour course on AWS Training platform. It has the fault of being service-oriented and you can think of it as a light version of the AWS Security Speciality.
Microsoft Azure
Microsoft Azure has the most built-in security toolings out of all the CSPs, so you're leaning less on third-party security providers and I think the reason for this is because Microsoft is a hot-mess with so many sprawling services offerings if they didn't have the built-in tooling it would just be a security nightmare.
While AWS documentation focuses on each service and its utility, Microsoft documentation focuses heavily on business applications and for Security, they have lots of great content.
Microsoft Security Best Practices
I would strongly recommend Microsoft Security Best Practices which is both a video series and a PowerPoint document.
Microsoft Security Certifications
Microsoft Azure has multiple role-based security courses:
- SC-900, AZ-500, SC-300, SC-400, SC-200
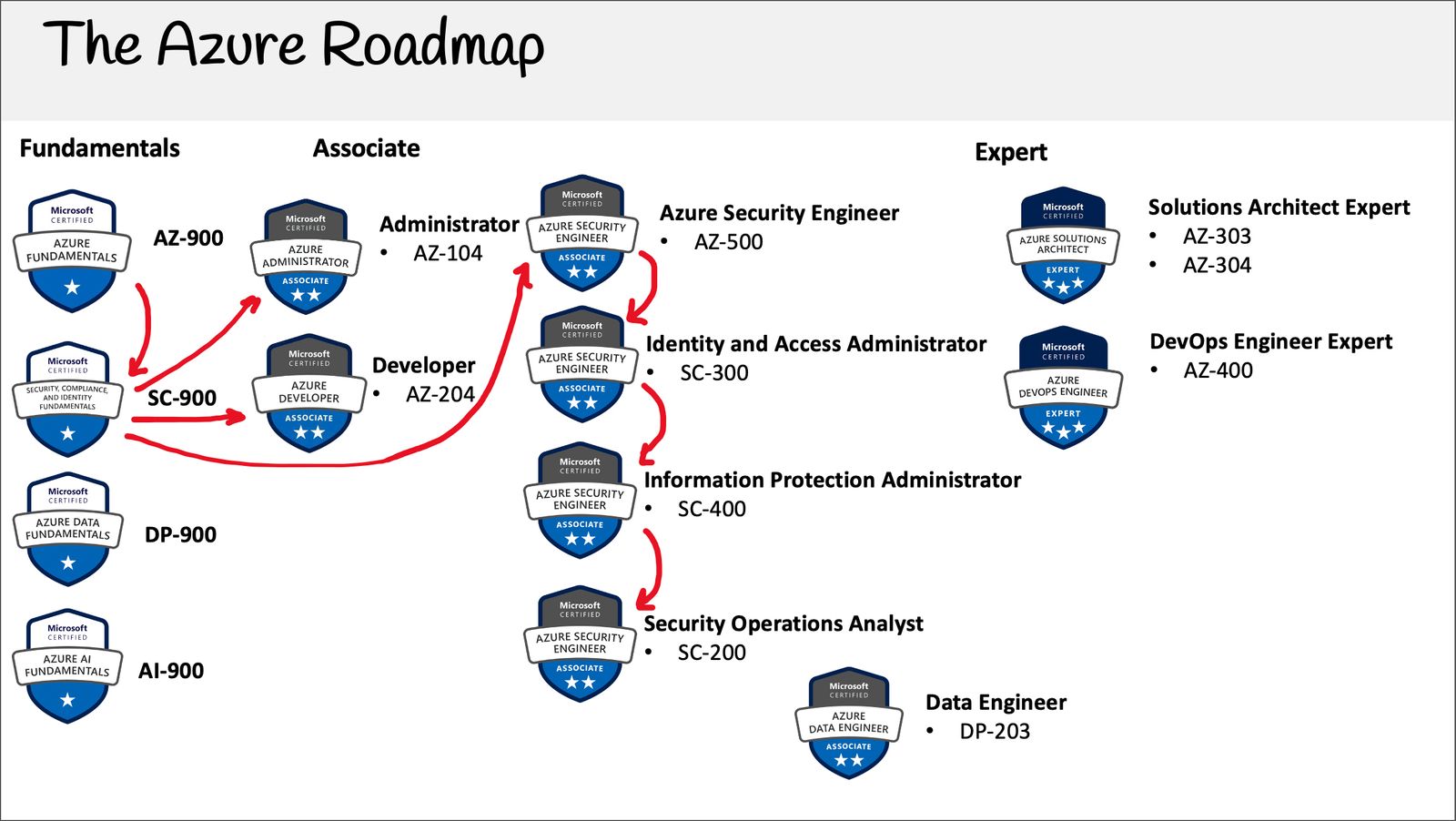
If you take the SC-900 it's a broad introduction that touches a bit of everything which is covered in the associate security courses.
Honestly, Azure should have just taken all those associates and rolled it into a Professional or Speciality.
Azure has a huge focus on Active Directory and Identity since Azure AD is their flagship product.
There is a free learning path by Microsoft on Microsoft Learnbut I feel just like AWS they gloss over lots of security fundamentals.
I created a free SC-900 study course but my real motivation was to create a Cloud Security Primer that I front-loaded into the course. At some point I will extract that secret course and expand it into a practical cloud-agnostic security course.
Google Cloud
GCP is interesting in that its service offering is lean by design, and for that reason, security is a breeze on GCP.
GCP has been ahead of the game in many regards. For example, GCP doesn't have isolated GovCloud regions in the same sense as Azure or AWS. Many GCPs regions by design can handle FedRamp workloads and will be either designated appropriate for workloads that are High or Medium baselines.
GCP also has their own security key called Titan

Are Titan keys superior to YubiKeys? That's debatable but it's cool that Google makes their own.
Professional Cloud Security Engineer Certification
GCP has one certification for security the Cloud Security Engineer. Despite being called a Professional Certification it's not that difficult, but it's a well-balanced cloud security certification, unlike AWS which is more DevSecOps and Azure with focuses too much on Identity.
Additional Practical Cloud Security Content
INE
INE has a good mix of practical cloud security content. Their platform is $49 USD per month, you could probably consume most of what you need in a month and then unsubscribe.
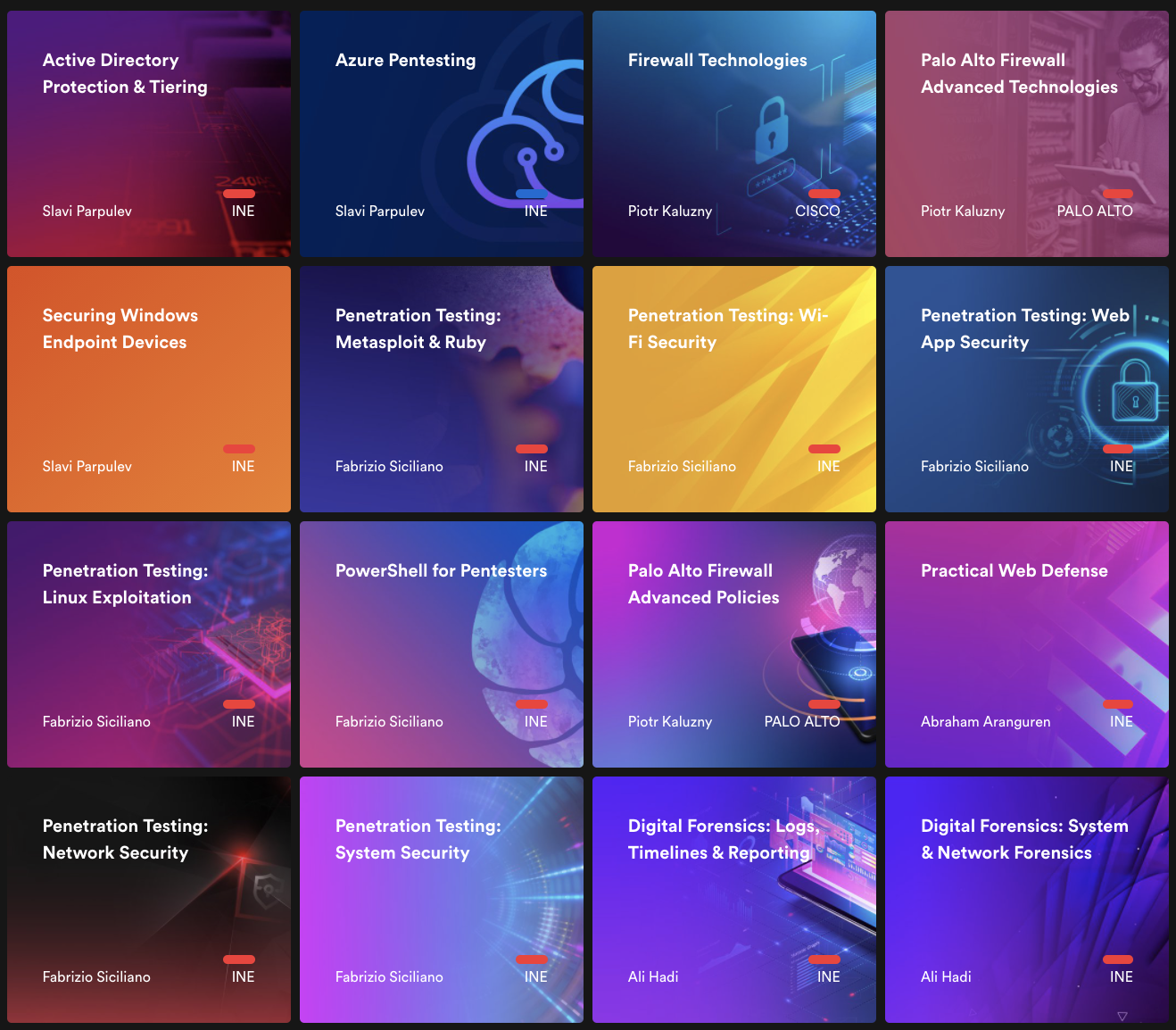
If you want to inquire more about INE offerings, go and DM Tracy and tell them Andrew Brown sent you.
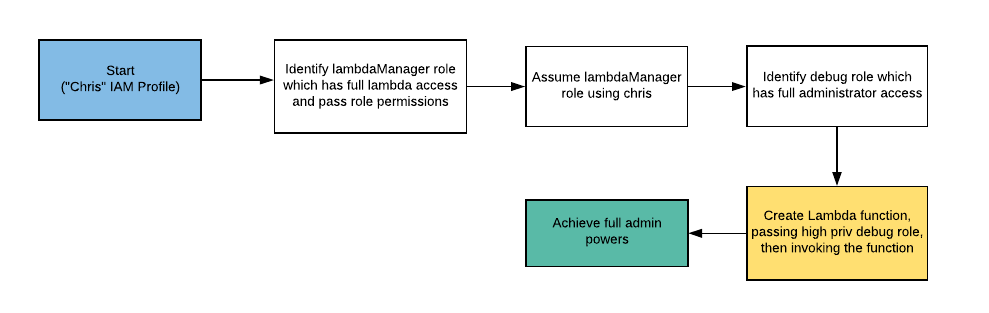
Rhino Security Labs and Cloud Goat
Rhino Security Labs is always putting out great content and open-source projects. One I like very much, in particular, is their project Cloud Goat.
CloudGoat allows you to provision a "Vulnerable by Design" AWS environment so that you pretend to be a malicious actor trying to find your way in.
If you get stuck and you want to see the answer they have these Exploitation Routes:
Conclusion
The Security industry is flush with security certifications but I feel there Cloud Security has quite a few holes yet to be filled with an end-to-end training solution.
There is no definitive path to a Cloud Security role, there are lots of bits and pieces all over the place and you need to patchwork together your own solution.
I mention a bunch of different paid providers, but I am not sponsored by anyone, no receive affiliates (at least at the time of writing this article). If anyone want to send me t-shirts, I take a large.